
In the past week (March 9–16, 2026) several events underscored how destructive cyber‑attacks, vendor missteps and delayed notifications continue to challenge HIPAA compliance and patient safety. The U.S. regulatory landscape was quiet, but multiple breach notices and a major cyber‑attack revealed vulnerabilities in mobile‑device management and vendor oversight. Below we recap the key events and provide recommended actions for compliance teams.
Regulatory & Legal Updates
Quiet week on new OCR settlements; ongoing emphasis on risk analyses
The HHS Office for Civil Rights (OCR) did not announce new HIPAA settlements this week. The most recent settlement remains the March 5 corrective action plan with dental marketing firm MMG Fusion LLC over a 2020 breach that exposed 15 million patients (covered in last week’s newsletter). Compliance teams should continue to focus on thorough risk analyses and prompt breach notifications as required by HIPAA.
Breach & Incident Notices
CenterWell senior‑care network breach
What happened: CenterWell, a Louisville‑based senior‑care provider with clinics and pharmacies in 30 U.S. states, reported a data breach to the Texas Attorney General on March 6, 2026. The HIPAA Journal notes that the unauthorized access compromised personal and protected health information of at least 4,618 Texas residents; the company provides services nationwide so the total number of affected patients may be substantially larger. Data involved includes names, addresses, dates of birth and medical information. As of mid‑March, CenterWell had not yet sent notification letters to affected individuals and no threat group has claimed responsibility.
Why it matters: The delayed notification increases the risk that patients cannot take timely steps to protect themselves. HIPAA requires covered entities to notify affected individuals without unreasonable delay and no later than 60 days after discovery of a breach. Failing to meet these timelines can increase regulatory penalties and litigation risk.
Recommended actions:
- Conduct a root‑cause analysis to determine how unauthorized access occurred and close the vulnerabilities.
- Prepare notification letters now to comply with federal and state breach‑notification deadlines.
- Review vendor and IT support agreements to ensure clear obligations for security and prompt breach reporting.
Bell Ambulance breach report
What happened: Milwaukee‑based Bell Ambulance disclosed that a February 2025 cyber‑attack by the Medusa ransomware group exposed the data of 237,830 individuals. Security Affairs reports that attackers infiltrated Bell’s network between February 7–14, 2025, claimed to have stolen over 219 GB of data and posted the data online. Bell completed its investigation on February 20, 2026 and notified the Maine Attorney General, revealing that compromised information included names, Social Security numbers, birth dates, driver’s‑license numbers, financial information, medical data and health insurance details. The company reset passwords, secured accounts and is offering 12 months of free credit monitoring.
Why it matters: Although the intrusion occurred in 2025, the breach was formally reported this week, illustrating how vendor and operational delays can push notifications well beyond the attack itself. Large ambulance services may handle sensitive PHI and payment information for multiple hospitals and insurers; compromise of such data can lead to identity theft and fraud.
Recommended actions:
- Review incident‑response timelines and ensure your organization’s contracts require business associates to inform you promptly when breaches occur.
- Verify that credit‑monitoring services offered by vendors meet industry standards and ensure affected individuals understand how to enroll.
- Validate that your own organizations’ emergency and transport partners follow strong cybersecurity practices and multifactor authentication.
Other breach notifications and updates
North Central Behavioral Health Systems (Illinois) – An employee email account compromise discovered in December 2025 may have exposed patient data, including names, addresses, dates of birth and clinical information. Investigations are ongoing and affected individuals are being notified.
College of Health Care Professions (Texas) – The Texas Attorney General was notified that a breach may have compromised sensitive information for 68,825 individuals, including Social Security numbers, driver’s‑license numbers and medical/insurance data.
NADAP/NYC Health + Hospitals – The city’s care‑management partner reported that a November 2025 cyberattack exposed names, Social Security numbers, treatment plans, diagnoses, medications and Medicaid ID numbers for 5,086 patients. NYC Health posted a public breach notice on March 11, 2026.
Cybersecurity Alerts & Best‑Practice Insights
Destructive wiper attack cripples Stryker
What happened: On March 11, 2026 medical technology giant Stryker suffered a global network disruption. An advisory by the American Hospital Association (AHA) notes that the company’s Microsoft environment was affected; Stryker said there was no evidence of ransomware or malware and believed the incident had been contained. AHA national cybersecurity adviser John Riggi said that while there were no immediate disruptions to U.S. hospitals, supply‑chain impacts could emerge as hospitals evaluate services and technology linked to Stryker.
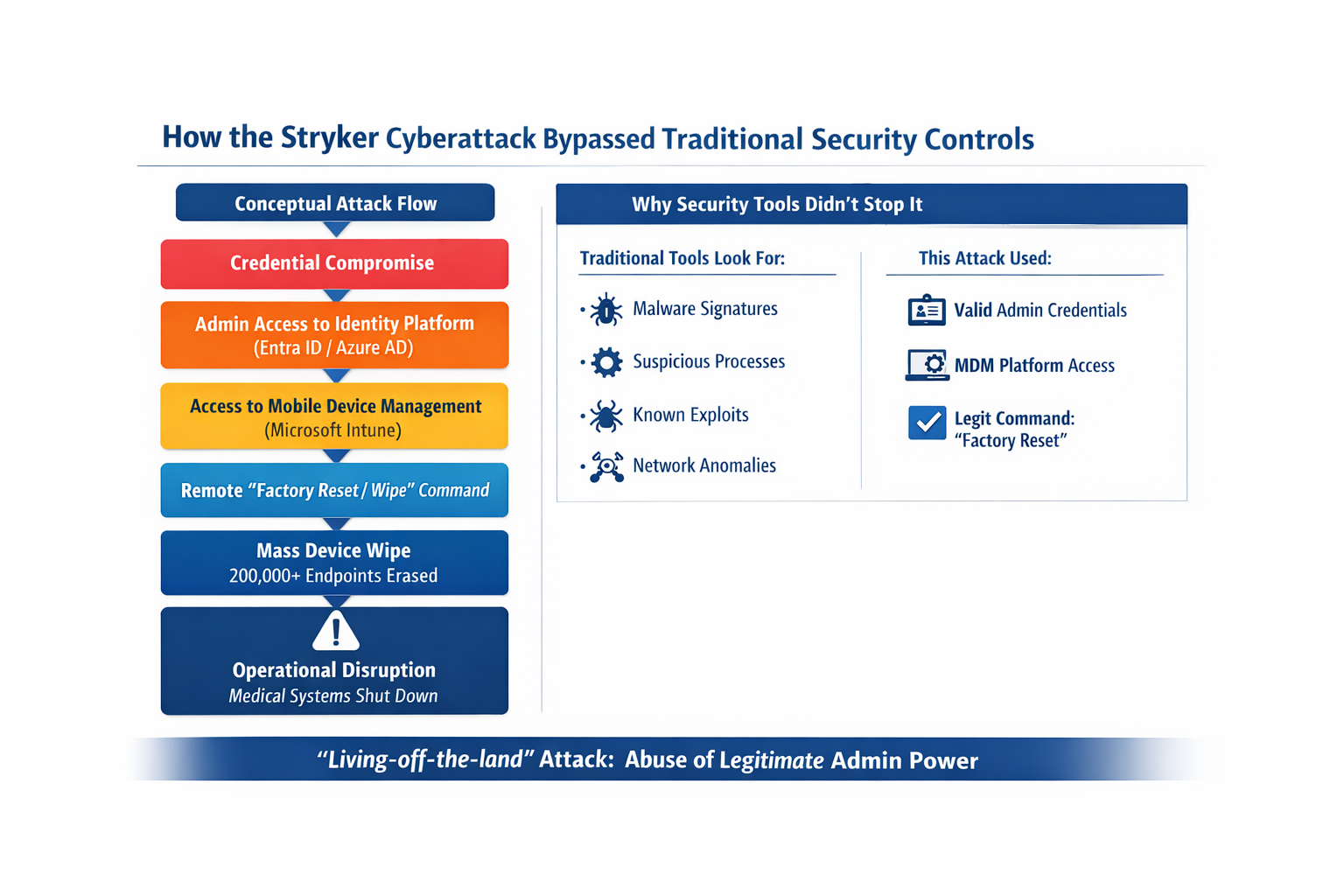
Attack details: A subsequent technical analysis revealed that the incident was not a typical ransomware event but a destructive wiper attack claimed by Handala, a hacktivist group linked to Iran. In a detailed post‑mortem, Shieldworkz reports that Handala remotely wiped over 200,000 devices across 79 countries, defaced login screens with its logo and claimed to have exfiltrated 50 terabytes of data. The attackers gained administrative access to Stryker’s Microsoft Intune mobile‑device management (MDM) platform and used its legitimate “remote wipe” capability to factory‑reset every enrolled device. This meant no malware signatures were detected—Intune executed the wipes as if they were authorized IT commands.
Patient‑safety impact: The wiper attack disrupted LIFENET, Stryker’s electrocardiogram‑transmission system used by emergency responders. Maryland’s Institute for Emergency Medical Services reported that LIFENET was non‑functional across most of the state, forcing crews to revert to radio consultation. The attack also wiped personal devices enrolled under Stryker’s bring‑your‑own‑device (BYOD) policy, leaving employees without banking apps or authenticator tokens.
Why it matters: This incident illustrates how supply‑chain attacks can harm patient care even when the healthcare provider itself isn’t breached. Hackers exploited legitimate administrative access rather than malware, highlighting gaps in MDM security and privileged‑access controls. The LIFENET outage shows that cyberattacks on vendors can directly disrupt emergency care.
Recommended actions:
- Harden MDM platforms and enforce least‑privilege access. Restrict who can issue remote‑wipe commands; monitor Intune/MDM logs for unusual activity; require multifactor authentication for admin accounts.
- Segment critical clinical systems. Keep patient‑facing applications like ECG transmission separate from corporate IT networks so a vendor incident does not take down vital services.
- Revisit BYOD policies. Consider limiting MDM enrollment on personal devices or providing separate work devices to prevent personal data loss during remote‑wipe events.
- Prepare for supply‑chain outages. Test downtime procedures for third‑party systems and ensure backup communication channels (e.g., radio consultation) are ready if vendor platforms fail.
- Enhance vendor due diligence. Verify that business associates maintain robust incident‑response capabilities, including the ability to coordinate with law enforcement and notify customers promptly.
Trend: Vendors and MDM tools as top risks
This week’s developments reinforce that compliance teams must look beyond traditional ransomware defenses. The CenterWell and Bell Ambulance breaches highlight how delayed notification and inadequate vendor oversight can expose patients long after an attack. The Stryker incident shows that destructive attacks can leverage legitimate MDM capabilities, catching organizations off guard and directly impacting patient care. To stay ahead:
1) Audit your MDM configurations and BYOD policies to ensure remote‑wipe functions cannot be abused. Maintain separate work devices for critical roles where possible.
2) Strengthen business associate agreements to include rapid breach notification, clear liability for data security and requirements for multifactor authentication and network segmentation.
3) Practice supply‑chain downtime drills. Ensure that clinical teams can continue operations if a vendor’s systems go offline unexpectedly.
Final Thoughts
Although no new OCR enforcement actions were announced, this week underscores that regulatory penalties are only one piece of the compliance puzzle. Slow breach notifications, vendor missteps and sophisticated supply‑chain attacks can all trigger significant legal and patient‑safety risks. By prioritizing risk assessments, vendor management, MDM security and incident‑response readiness, compliance teams can better protect patients and reduce exposure to regulatory and litigation consequences.
